Tech Tip Tuesday (March 3, 2026)
🛡️ Safety Beyond the InboxInbox! 🛡️
Yes, we've had phishing. But what about second phishing?
While we’re all getting better at spotting "phishy"phishy" emails, scammers arehave movingmoved into the physical world. From QR codes to "lost" USB drives, they are finding new ways to bypass our digital filters.
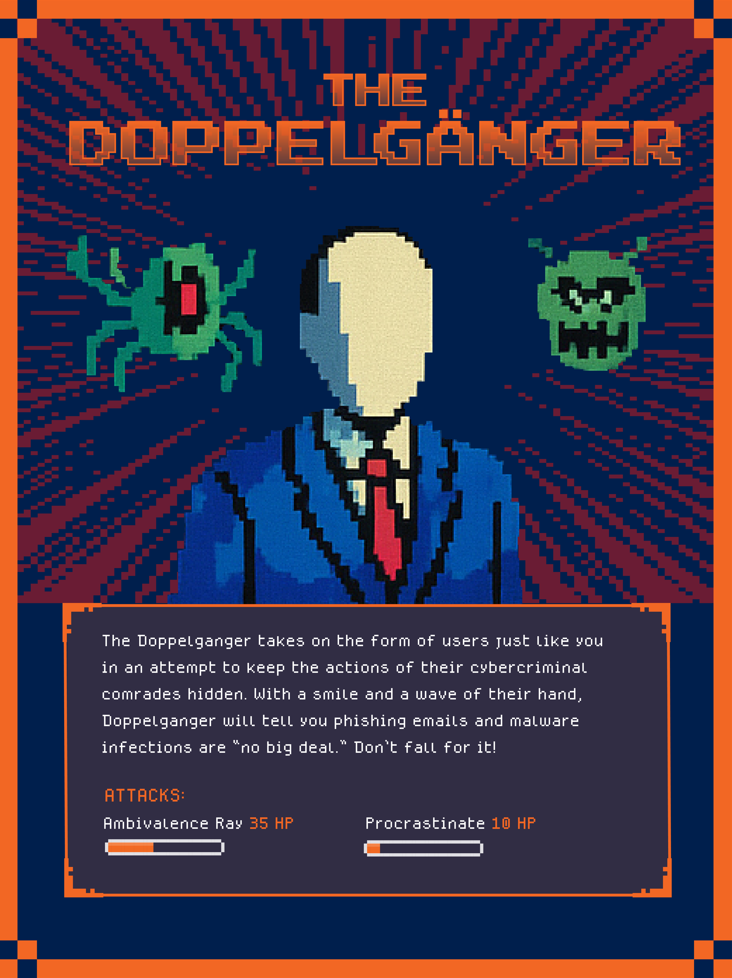
Meet "The DoppelgängerMimic" — Master of Physical Deception 🎭
The Mimic doesn't need to hack your firewall; they just need to hack your curiosity. By leaving a "lost" USB drive in the parking lot or a helpful-looking QR code sticker on a breakroom table, they wait for you to take the bait.
They rely on the fact that teachers and staff are naturally helpful. Once you plug in that mystery drive to "find the Artowner" ofor Socialscan Engineeringthat code to "see the staff discount," The Mimic bypasses district security and gains instant access to sensitive student or staff data.
Their Goal: To catch you off guard when you are away from your computer and feeling helpful, curious, or in a hurry.
The "Mimic" 3-Second Safety Check 🛑
MeetBefore you scan or plug anything in, run through these three quick questions to see if The Doppelgänger!Mimic Thisis trying to hook you:
1. Is it a "Layer"? Look closely at the QR code. Is it printed directly on the poster, or is it a sticker slapped over the original? If it feels like a "top layer," do not scan it.
2. Does the "Preview" match? When you hover your camera over a QR code, your phone shows a URL preview. If the link is acyberbunchtricksterofwhorandomdoesn’t hack computers. He hacks people. Through emails, texts, phone calls,gibberish orevenaface-to-face"shortener"conversations,(likesocialbit.lyengineersorusetiny.cc)trust,whenfear,itandshouldurgencybe a school website, close the app.
3. Is it "Unattended"? A USB drive sitting on a cafeteria table or a QR code on a random telephone pole is a red flag. If it’s not physically attached totrick you into giving up passwords, clicking links, or letting them in the door.
They might impersonateacoworker,trustedasource,vendor,leaveoritevenalone.
 |
|